Three Thoughts on Cyber and the Defense Department’s Report on the Chinese Military
More on:
The Defense Department released its annual report to Congress on Military and Security Developments Involving the People’s Republic of China 2013. Besides being delivered relatively early compared to past editions and being almost twice as long as the 2012 version, this year’s version has at least three interesting points about Chinese cyber activities.
First, as many have noted, the sharpest break from the past is that the report directly ascribes blame for cyberattacks to the Chinese government and military, saying, “numerous computer systems around the world, including those owned by the U.S. government, continued to be targeted for intrusions, some of which appear to be attributable directly to the Chinese government and military.” The 2012 report, by contrast, speaks of attacks “which originated within China” and active and persistent “Chinese actors.” The 2011 report describes cyber intrusions, “some of which appear to have originated within the People’s Republic of China (PRC).” The 2010 report seemed to split the difference, stating it was “unclear if these intrusions were conducted by, or with the endorsement of, the People’s Liberation Army (PLA) or other elements of the PRC government.”
Second, as David Sanger notes in the New York Times, the report tries to describe Chinese thinking about offensive cyber operations by citing two works of military doctrine, “Science of Strategy” and “Science of Campaigns.” This is not new—the 2011 report mentions them by name, while the 2010 report uses the same phrase “authoritative PLA military writings.” Sanger uses the report’s claim that neither Chinese document “identifies specific criteria for employing computer network attack against an adversary” to turn the mirror back on its authors, and note that the Defense Department has also been opaque about the conditions under which it would employ offensive capabilities. This lack of transparency is extremely destabilizing; the military doctrine of both countries emphasizes the importance of early attacks to gain information dominance, creating intense pressure to “use it or lose it,” but there is little knowledge of the other sides’ red lines and how they might escalate.
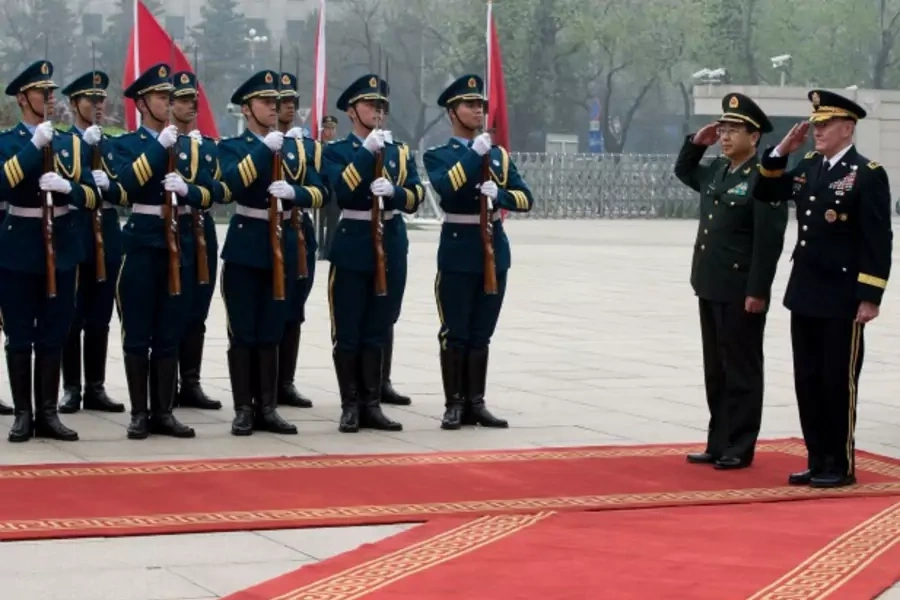
Third, despite the announcement of a U.S.-China working group on cybersecurity during Secretary of State John Kerry’s visit to China, and General Fang Fenghui’s declaration that China was willing to set up a cyberserurity “mechanism” during a meeting with chairman of the Joint Chiefs of Staff, General Martin E. Dempsey, the report does not give much reason for optimism that the two sides will find common ground on the rules of the road. For the first time, the report calls China out for playing a “disruptive role in multilateral efforts to establish transparency and confidence building measures in international fora such as the Organization for Security and Cooperation in Europe, Association of Southeast Asian Nations Regional Forum, and the United Nations Group of Governmental Experts.”
Mistrust between the two sides was always going to make cooperation hard. The week before General Dempsey’s visit, the PLA Daily ran a piece with the headline, “U.S. Cybersecurity Strategy is Fake Cooperation and Real Confrontation.” Playing a spoiler in international meetings, however, suggests how broad and deep the divide really is.
More on:
 Online Store
Online Store