Year in Review: Chinese Cyber Sovereignty in Action
2017 was a year of great energy and activism for China in cyberspace, with the Chinese leadership pushing on three interconnected fronts: information control; cybersecurity; and international norms and diplomacy.
By experts and staff
- Published
 Adam SegalCFR ExpertIra A. Lipman Chair in Emerging Technologies and National Security and Director of the Digital and Cyberspace Policy Program
Adam SegalCFR ExpertIra A. Lipman Chair in Emerging Technologies and National Security and Director of the Digital and Cyberspace Policy Program
2017 was a year of great energy and activism for China in cyberspace. In its efforts to turn the country from a “big cyber power” into a “cyber superpower,” the Chinese leadership was active on three interconnected fronts: information control; cybersecurity; and international norms and diplomacy.
While many of the new restrictions on the domestic internet were rolled out during the run up to the party congress, the moves were more than symptoms of nervousness about the installation of new leaders ahead of the 19th Party Congress. Rather, they reflected a multi-year trend of tighter controls on online speech and civil society. In March 2017, Tencent and other companies were told to close websites that hosted discussions on the military, history, and international affairs. In July, telecoms were told to crack down on “illegal” VPNs (in response, Apple was forced to remove VPNs from the China app store). A month later, the Cyberspace Administration of China announced new regulations further limiting online anonymity. The country also demonstrated new technological prowess, censoring photos in one-to-one WeChat discussions and disrupting WhatsApp. Parallel to the tightening on social media, Beijing has deployed facial and voice recognition, artificial intelligence, and other surveillance technologies throughout the country (See the excellent coverage in BuzzFeed and the Wall Street Journal of how these technologies are used in the restive province of Xinjiang at their most dystopian).
Central to the program of defending cyber sovereignty and building China into a national power in cyberspace is the cybersecurity law, which went into effect on June 1. Much about the law remains uncertain as the government develops standards and domestic actors debate how it should be implemented, but the greatest sources of concern for foreign technology companies are restrictions on outbound data transfer, the definition of “critical information infrastructure”, and network-equipment security reviews. While Chinese officials have promised greater transparency in implementing the rules and assured companies that the goal of the law is not forced technology transfer, the rules are bound to be a source of major friction in 2018, especially as the Trump administration concludes its Section 301 investigation of China’s theft of intellectual property.
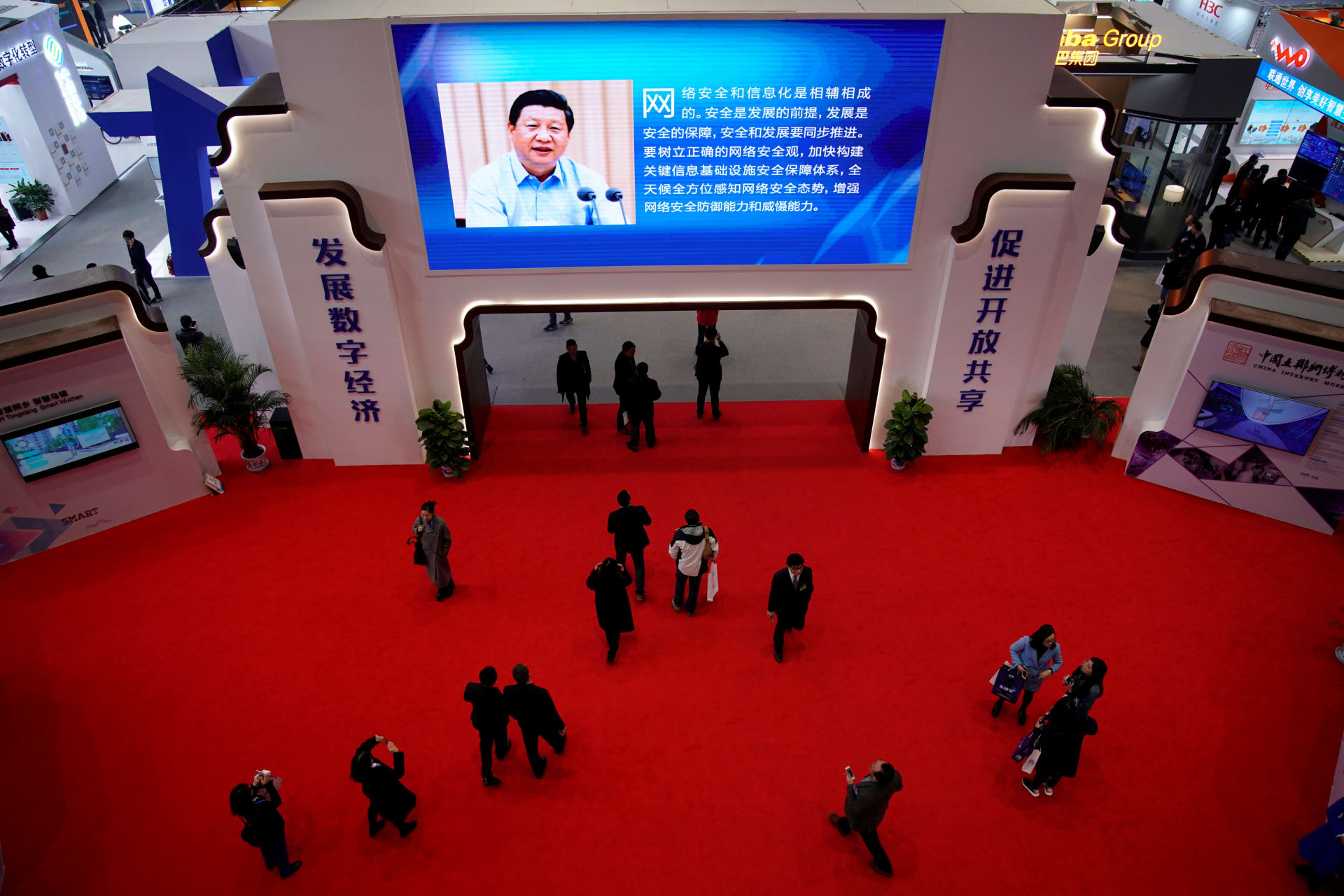
Beijing has also worked this year to push the concept of cyber sovereignty internationally. After the deadlock of the discussion on what constitutes acceptable nation state behavior among a group of government experts at the United Nations, China has doubled down on the argument that the UN should play a central role in developing international norms of cyberspace. China also held the 4th World Internet Conference in Wuzhen, hosting Apple’s Tim Cook and Google’s Sundar Pichai for the first time. The Apple CEO’s speech in particular raised eyebrows, with Cook, a vocal defender of privacy and free speech at home, proclaiming that the company shared China’s vision for “developing a digital economy for openness and shared benefits.” The sense of Beijing’s forward momentum was heightened by what might be generously called a pause in U.S. cyber strategy (or what my colleague David Fidler calls “disruption”) as the State Department re-organized its cyber operations.
The great uncertainty of 2018 is whether it will see a return of the cyber espionage issue in Sino-U.S. relations. Since seeing a notable decline in the number of hacks after the 2015 agreement between President Obama and Xi, cybersecurity companies this year reported an uptick in Chinese operations. In November 2017, the Department of Justice indicted three Chinese employed by Boyusec for hacking into the computers of Moody’s Analytics, Siemens AG, and GPS navigation company Trimble Inc. While Boyusec is known to contract with the Ministry of State Security, U.S. officials made no claims about state sponsorship of the cyber attacks. The Chinese may be backsliding on the agreement, or exploiting some of its ambiguities, but it would not be surprising if there is a notable increase in tensions between the two sides over trade or North Korea, to see the number of hacks continue to rise.