Ransomware’s Path to Product/Market Fit
The economics of cybersecurity have long benefited attackers, but ransomware has become so successful that if these criminal gangs running the attacks were viewed as startups, they would all be unicorns.
By experts and staff
- Published
For over a decade, foreign actors have deployed backdoors in American networks, and when caught, foreign official deny culpability and senior U.S. leaders are quietly briefed on the damage and possible responses. However, while this sequence of events is often painted as an “impending cyber war,” identifying the proverbial ‘digital first strike’ from foreign adversaries has proven to be a waiting game. In fact, the quiet proliferation of cyber weapons into the hands of criminals targeting critical infrastructure has regularly been overlooked. Instead of a sudden catastrophic attack, the current reality of our cyber-environment is one where an undeterrable threat exists, driven by the cold hard logic of criminal economics. The economics of cybersecurity have long benefited attackers, but ransomware has become so successful that if these criminal gangs running the attacks were viewed as startups, they would all be unicorns.
Over the past two years, ransomware attacks have targeted organizations more likely to pay out due to their critical requirements for uptime, sensitivity to data leaks, and deep pockets. The result has been a shift away from smaller organizations paying a few thousand dollars, towards pipelines, food suppliers, and hospitals pressured into paying millions of dollars.
According to a recent report by the Ransomware Task Force, in 2020 alone there was a 311 percent increase in the amount of funds extorted (total revenue of $350 million), a 171 percent increase in the average payment (average extortion price of $312,493), with at least 2,400 new “customer-victims.” As bad as they are, these figures are widely accepted to be the tip of the iceberg due to a lack of willingness by companies to admit to being victims and that the total reported incident costs do not include downtime, forensic response, and information technology (IT) equipment replacement.
Like many breakout startups, ransomware’s profitability has exploded thanks to three critical trends.
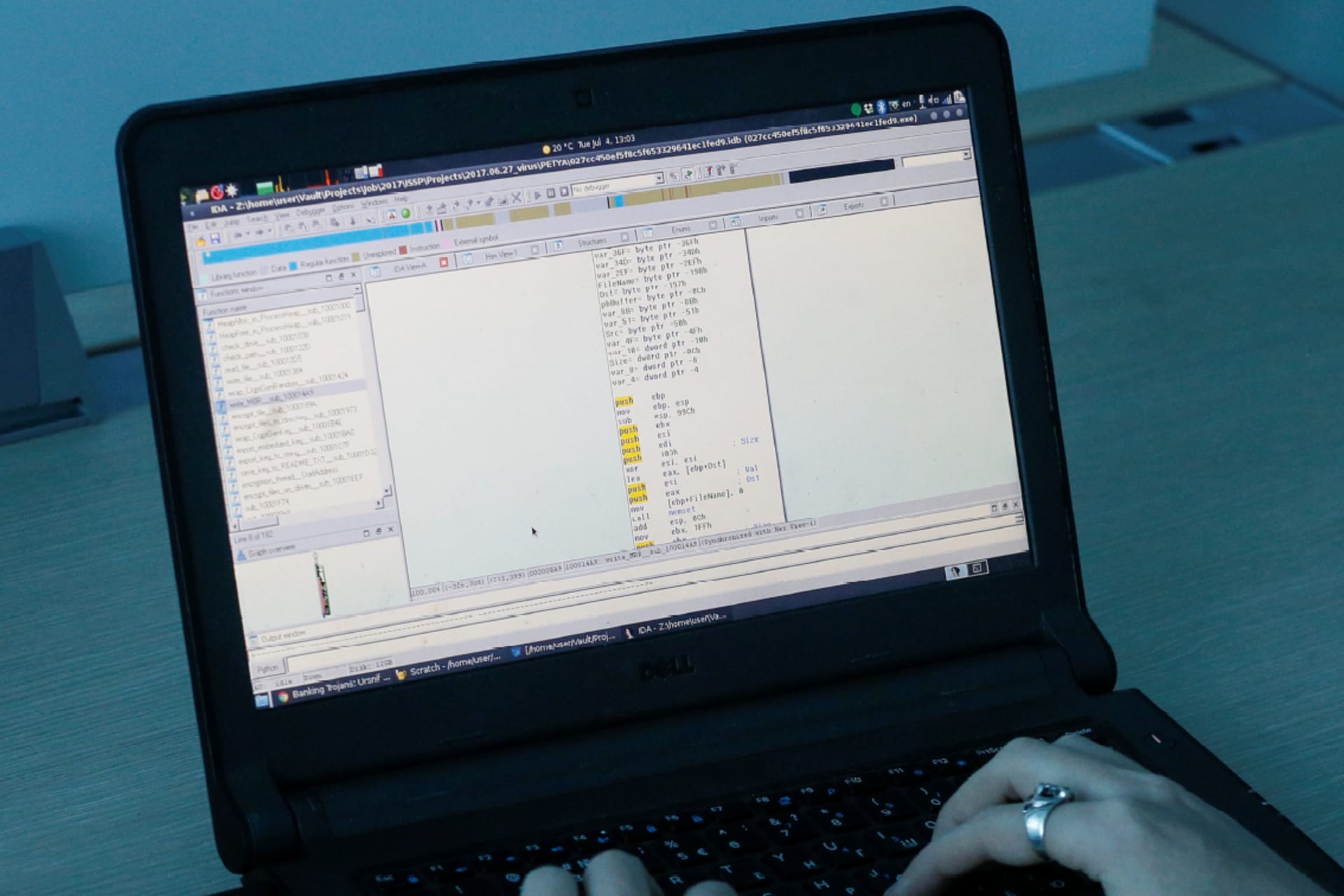
Innovation in a proven product. The creation of an online platform and workflow for ransomware-as-a-service (RAAS) has brought ‘Initial Access Brokers’ into the limelight. The creation of a ransomware supply chain allows for the separation of customer service from specialized malware development and initial access to victim networks (run by specialized Initial Access Brokers).
Decreased cost of production. The franchising of ransomware access brokering allows for more experienced hackers to deploy sophisticated attacks to gain entry into a corporation and then sell the access to less experienced criminals to conduct the extortion. This production line approach indicates the skill necessary to conduct an attack has dropped significantly, making it cheaper and easier to scale the deployment of ransomware attacks.
Larger payouts and increased revenue. Ransomware actors have refocused their attacks towards victims in industries that would be most harmed by business interruption. These victims generally also have the ability to pay a larger extortion. Recently, targeting has focused on midsize to large manufacturers, service providers, and critical infrastructure like hospitals, cities, and energy firms.
A savvy venture capitalist would say ransomware gangs have “crossed the chasm” of a niche product and have now found “product/market fit (PMF),” meaning they understand who their target customers are and are successful at “selling” their product. Unfortunately, that product is extortion and their most successful markets are industries that have been slow to adopt new security standards or allocate appropriate investments in cyber hygiene. This further lowers the cost of the deployment of ransomware and increases criminals’ ability to focus on perfecting extortion negotiation and “marketing” around the fear of being hit.
Another sign of PMF is the sophistication of ransomware criminals’ efficient and effective marketing. With just a few well-placed interviews and big payouts, they have managed to punch above their weight and ride a wave of attention in the press that has driven international level awareness, sparking serious interest by top national leaders.
With such a booming business model, ransomware seems like an unstoppable force. But like any unicorn, it can be brought down by significant shifts in their market. The ransomware business model can be disrupted by increasing the cost of transactions. Transaction fees are not favored by many, but criminals are willing to accept significant transaction costs in exchange for anonymity by dealing in cryptocurrency. Expanding the ability to clawback payments could increase the probability of criminals facing a loss on transactions. Recently, the U.S. Department of Justice has worked with crypto analysis companies to trace transactions and even seize assets, like in the Colonial Pipeline attack. While this capability depends mostly on advanced intelligence and luck, private cyber insurance companies that often have to pay out for these ransoms could be financially incentivized to drive a new private market for recovering stolen crypto assets. There are already various tactics under discussion for making this a reality.
Policy makers can also work to increase the cost of production. Few public indictments have been brought against ransomware criminals due to a lack of strong evidence and cooperation with the countries in which they reside. Their assets, however, are often docked in countries that would cooperate with western law enforcement. If criminals are identified publicly, civil asset seizure could become more feasible, even creating a secondary market for trading information that leads to the attribution of actors. To this point, the Joe Biden Administration has already taken the first step by offering a $10 million bounty for information on ransomware actors.
In addition, the public and private sector can reduce the supply of victims. Ransomware preys on poor cyber hygiene by leveraging small mistakes to deploy malware and provide attackers access to sensitive data. Increasing cyber hygiene broadly has been a Sisyphean task since the early days of the internet due to motivated human attackers, increasingly complex networks, and view of security as a “nice-to-have” in many industries. The Biden Administration is continuing a long-standing effort to change these dynamics by pushing their own IT suppliers to provide better security, hoping this will have a knock on effect in the private sector markets as well. The president and his cabinet also recently convened a meeting of top infrastructure, technology and insurance companies to discuss building better cyber standards and incentives.
Aside from policy levers, we also have historical economic models that provide some templates for success. The rise in kidnappings of businessmen traveling to South America in the seventies and eighties went through a similar boom as ransomware, only it directly threatened people’s lives. In the case of kidnapping, the insurance industry responded to market forces by raising underwriting standards that encouraged training and security as requirements for kidnap and ransom (K&R) policies. At the same time, the insurance providers worked together to lower the prices paid out on ransoms until it was no longer profitable to hold hostages in exchange for an insurance policy payout.
Insurance companies have recently been criticized for exacerbating ransomware, by covering extortion payments in policies. However, banning payments would most likely have negative unintended consequences. The insurance industry instead needs to follow the template from K&R policies and do more to drive minimum cyber hygiene standards among their insureds and share information on what is effective in making companies resilient to extortion attempts. This should be a commitment from the entire cyber insurance industry.
The tools exist, there are historical economic templates to follow, and most important, the pain has reached a level that demands a response. The choice is ours to either let this market failure continue or to pick up those tools and work to shift the economics towards a more secure and resilient internet. Smart money should be investing in a future where the economics favor the defenders.