The Right Response to SolarWinds
A strongly worded message has been sent to Moscow, but a forcible response that changes minds is elusive.
By experts and staff
- Published
- Guest Blogger for Net Politics
Dr. Scott Jasper is a lecturer at the Naval Postgraduate School in Monterey, California. He is the author of Russian Cyber Operations: Coding the Boundaries of Conflict.
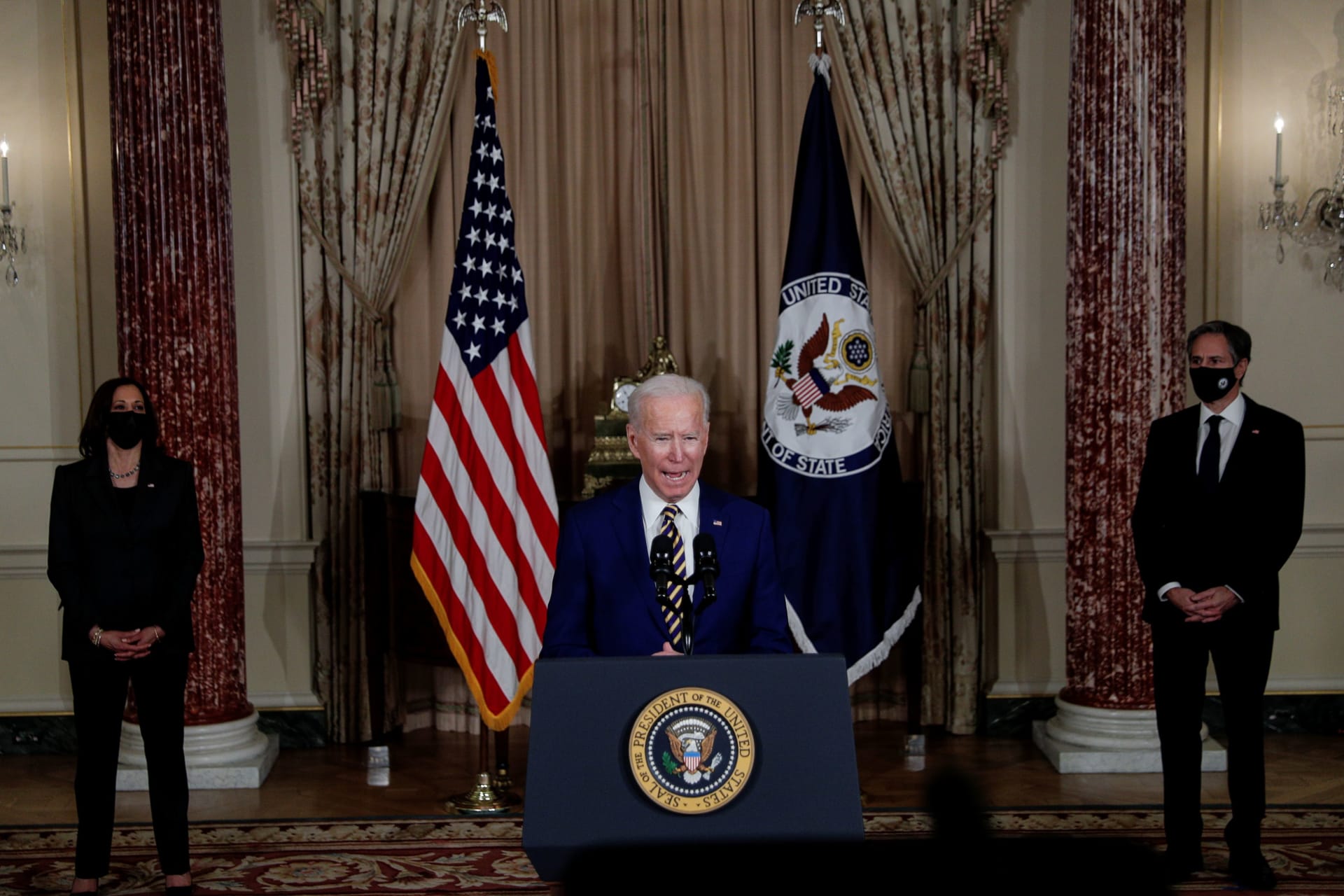
In a formal joint statement, four U.S. agencies in charge of intelligence and cybersecurity affirmed that an advanced hacking group, “likely Russian in origin,” is responsible for the SolarWinds Orion software compromise. President Biden has ordered a sweeping review of American intelligence on Russia’s role in the breach and reportedly told Putin that “that the days of the United States rolling over in the face of Russia’s aggressive actions — interfering with our elections, cyberattacks, poisoning its citizens — are over.” Taking a more assertive tone toward Moscow may be the easiest part of the White House’s reaction to the SolarWinds hack. Finding the right balance of effective offensive and defensive actions will be more difficult.
While the president has publicly vowed to make Russia “pay a price” for this significant cyber incident, his aides have reportedly cautioned him that because, at least for now, the operation appears to be an intelligence gathering effort, U.S. options for responding directly are limited. There is no express prohibition on cyber espionage in international law per se—and all nations, including the United States, do it. The Computer Fraud and Abuse Act (CFAA) [PDF] could be used to indict Russian state hackers for trespassing in government computers or obtaining national security information. The latter section of the U.S. legal code is infrequently used, partly because national security information is often classified and thus protected from exposure. Nonetheless, a 2001 case, United States v. Ivanov [PDF], shows that there is precedent and intent for CFAA applying extraterritorially to foreign hackers.
Sanctioning or indicting Russian state actors for cyber espionage, however, could set a dangerous precedent to be used against individual NSA or CIA hackers. Previously, the U.S. government has used sanctions in response to destabilizing activities by the Russian military, including election interference and destructive cyberattacks, such as the NotPetya attack. Indictments have been issued against Chinese military personnel for breaching the networks of U.S. companies and stealing trade secrets. If the United States sanctions or indicts for cyber espionage, others could do the same.
If Director of National Intelligence Avril Haines finds the SolarWinds operation was not limited to espionage, retaliatory cyber operations against Russian infrastructure could be another option. Back doors could have been inserted into compromised systems, allowing Russian hackers to alter data or shut down networks. Leveraging these in the future to produce destructive effects would be a violation of sovereignty per international law and justify countermeasures. Moscow appears to recognize this possibility and has issued a security alert to Russian businesses, warning of a possible retaliatory cyberattack by the United States.
However, direct retaliation is not without its own risks. Momentarily turning off the power in Moscow, which would certainly constitute “an appropriately strong response,” is also likely to cause unintended escalation. Moreover, Russia would quickly patch the vulnerabilities that allowed for such a visible attack, possibly burning access and eliminating the means to conduct an attack when it really counts, like in a major conflict.
A more suitable approach than retorsion would be degrading the Kremlin’s ability to repeat similar intrusions. Previous hunt forward operations in Europe to find Russian malware on allied networks by U.S. Cyber Command could serve as a model for mass malware inoculation. Through this process, Cyber Command teams have discovered malware on networks in Macedonia, Montenegro, and other countries and then publicly released the code to the cybersecurity community to help others avoid falling victim to it. The U.S. government has stepped up its malware inoculation efforts since the 2018 U.S. midterm elections by publishing technical details on previously undisclosed malware [PDF] used by Russian military intelligence, thereby making it harder for them to avoid detection.
The United States should also improve its cyber defenses. Erica Borghard shows that a resilience-based approach assumes some compromises are impossible to prevent. What matters is how organizations respond after they occur and combat post-compromise activity inside their networks. Most current security measures are insufficient to defeat a highly evasive attacker that uses multiple techniques to obscure their activity.
However, new cloud-centric solutions that leverage data correlation technologies for threat detection, investigation, and response promise better defense and increased resilience. These tools stop advanced threats with machine learning and behavioral analysis while providing an understanding of attack causality. They would also address supply chain attacks that download malware in software updates by detecting subsequent misuse of legitimate tools and command lines. Furthermore, by deploying these tools, victim organizations would be able to remedy cyber breaches without disrupting their operations. However, these emerging capabilities are admittedly expensive, and only those with large budgets can currently afford them.
The Biden administration says that it intends to take steps to hold Russia accountable for malign activities, including the SolarWinds incident, at a time and manner of their choosing. They believe imposing costs and consequences will have an effect on Russia’s behavior. A strongly worded message has been sent to Moscow, but a forcible response that changes minds is elusive, especially in response to cyber espionage. With limited means to induce fear of reprisal or failure, a formidable commitment to U.S. cyber defenses is warranted to stop the next breach before harm is done.