Weighing the Risks of Remote Voting Technology
As the United States attempts to ensure that its citizens can safely vote during the COVID-19 pandemic, some have suggested that it should embrace remote voting technologies. However, these systems present formidable security risks that endanger democratic elections.
By experts and staff
- Published
By
- Guest Blogger for Net Politics
Connor Fairman is a research associate in the Digital and Cyberspace Policy program at the Council on Foreign Relations.
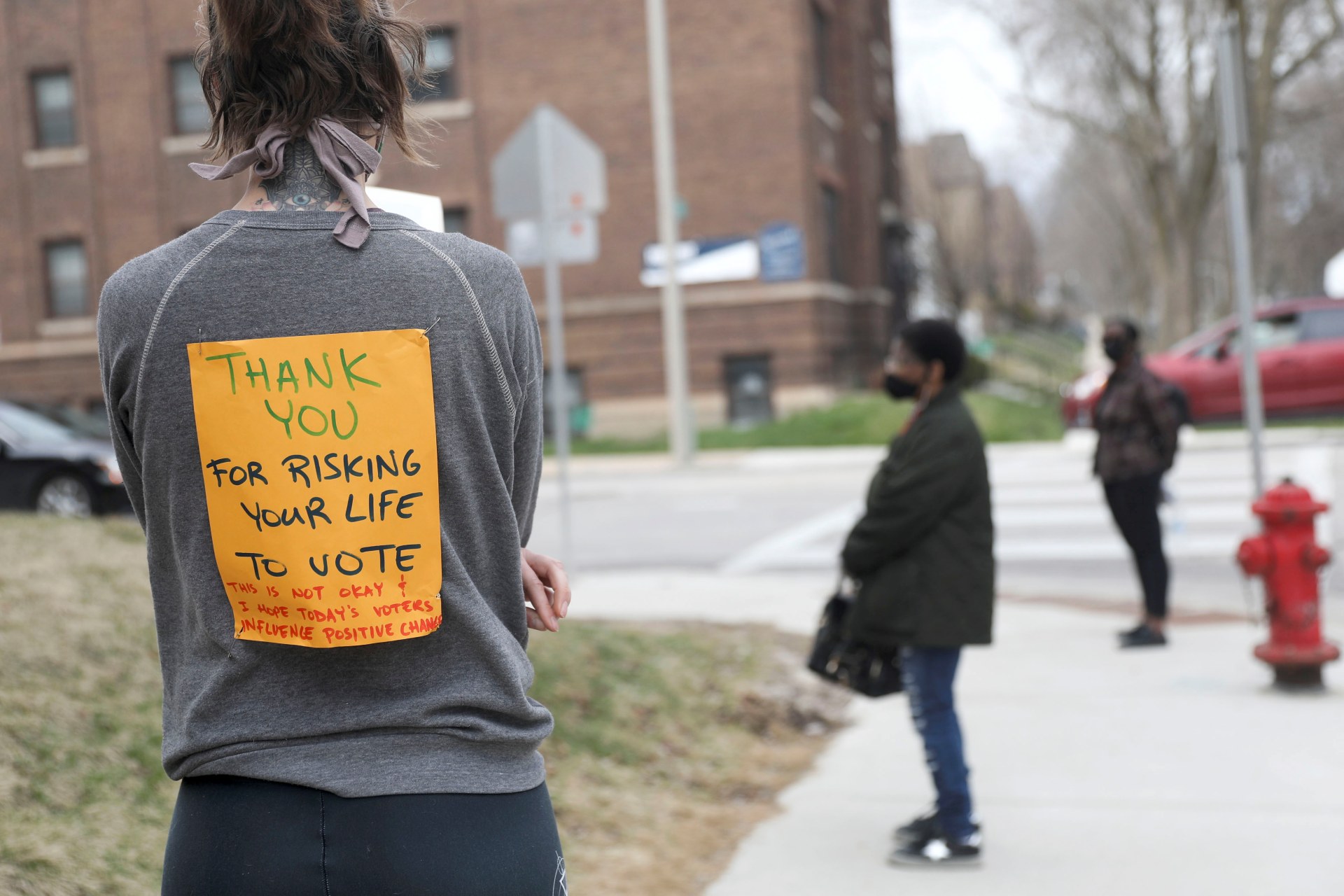
The spread of COVID-19 has raised serious questions about how Americans can vote without jeopardizing their health. The controversial Wisconsin primary held in early April, in which the state’s Supreme Court ordered election officials to proceed with in-person voting over the course of a single day, was plagued with long lines and crowding. This is exactly the opposite of the social distancing measures that have been put in place across the country to control the virus. Moreover, poor and minority communities in particular appear to have been confronted with a choice between voting and risking their health, essentially disenfranchising large groups of voters. While the option of voting at polling stations during the pandemic still seems to be on the table, some have suggested allowing people to vote remotely over the internet instead of casting their ballot in person. Policymakers may want to consider some forms of remote voting, such as vote-by-mail, but remote voting technology poses formidable security risks.
We already have some experience with the ways remote voting technology can go wrong. The smartphone application IowaReporterApp turned the Iowa caucus into a public debacle by confusing precinct leaders and misreporting vote totals. Later reporting revealed that the app was alarmingly rudimentary and insecure, allowing voting results, passwords, and other sensitive information to be intercepted. Another app, Voatz, a blockchain-based remote voting platform that has been used in elections in West Virginia, also received substantial negative publicity after researchers at MIT discovered that it contained vulnerabilities that would allow an attacker to intercept, stop, expose, and alter a user’s vote.
Even if vulnerabilities in the remote voting apps were immediately addressed, the smartphones and computers on which these apps run are themselves insecure. Vulnerabilities are routinely discovered in device operating systems, and devices that run the Android operating system (45 percent of smartphones in the United States) frequently go unpatched for months even after updates are released. This is because manufacturers, like Samsung and LG, are responsible for updating their own devices. Sometimes, manufacturers don’t automatically offer operating system updates to products that have been on the market for over a year, and older models are usually not eligible to download them at all. Cybersecurity expert Dan Guido, for example, found that IowaReporterApp was allowed to run on a version of Android released in 2014. The individual apps that users download to their devices also have their own bugs that hackers can take advantage of. This results in millions of devices in the United States running software with known vulnerabilities.
In order to address the vulnerabilities in older devices, some experts, like Guido, have recommended only allowing devices running newer versions of software to use remote voting apps. While technically safer, this would be discriminatory in practice because it would allow people with newer, more expensive devices to vote from wherever there is an internet connection, while people who can’t afford them would be forced to choose between risking exposure to COVID-19 by voting in person or not voting at all.
Elections in the United States are decentralized; individual states, counties, and towns are responsible for securing them. Smaller towns are woefully unprepared to manage the security risks of electronic voting machines, not to mention the integration of remote voting products. Even in the best-case scenario that a county has its own staff dedicated to securing the cybersecurity of its elections and the help of the National Guard, it will be no match for a sophisticated foreign adversary with virtually unlimited resources.
The decentralization of U.S. elections also translates into a lack of oversight over companies that produce election technologies. Vendors are not required to undergo any federal testing or certification process to be deployed in elections, nor are they required to disclose their corporate structure, supply chain, or hiring practices. Under federal law, they are also under no obligation to disclose when they’ve been hacked. Thus, foreign adversaries can conduct operations against the supply chain [PDF] of an election technology to gain access to products before they are in the hands of local election officials and voters, and even if the victim company discovered the attack, it would not have to report it.
In order for a foreign adversary to undermine U.S. elections, all it would have to do is cause Americans to question the validity or integrity [PDF] of the voting process. The documented vulnerabilities in existing remote voting apps and the devices on which they run are likely enough to accomplish this without any need for sophisticated cyber operations. Even if these products function perfectly and aren’t compromised, they will likely add new barriers for voters to safely participate in elections during the coronavirus pandemic. Given the lack of federal oversight over the companies that produce remote voting technology, there should be no expectation that new products that emerge will be any safer. Instead of spending the limited funding provided by the CARES Act to prepare for remote voting over the internet, states would be better off putting it towards the estimated high costs of vote-by-mail, which is considered to be much safer.