Cyber Week in Review: September 18, 2020
TikTok and WeChat drama continues to unfold; DOJ announces indictments against pro-Iran hackers; Facebook and Twitter close accounts linked to conservative youth group disinformation campaign; DOJ charges Chinese hackers and two Malaysian businessmen in global cybercrime spree; and Ransomware attack could have led to hospital patient’s death in Germany.
By experts and staff
- Published
Experts
![]() By Adam SegalIra A. Lipman Chair in Emerging Technologies and National Security and Director of the Digital and Cyberspace Policy Program
By Adam SegalIra A. Lipman Chair in Emerging Technologies and National Security and Director of the Digital and Cyberspace Policy Program
TikTok and WeChat Drama Continues to Unfold
On Friday, the U.S. Department of Commerce announced that it will ban new downloads and updates to Chinese apps TikTok and WeChat in U.S. app stores beginning Sunday, September 20. It also plans to prohibit the provision of internet hosting services, content delivery network services, internet transit and peering services, and any utilization of the apps‘ constituent code, functions, or services in the United States effective September 20 for WeChat and November 12 for TikTok. The decision to extend these provisions for TikTok to November 12 will stall a complete ban of the app until after the presidential election and give the Committee on Foreign Investment in the United States more time to examine the proposed TikTok-Oracle deal. According to the proposed deal, TikTok will be listed on a U.S. stock exchanges, Oracle will own a minority stake of less than 20 percent of TikTok and be responsible for hosting and securing U.S. user data. Walmart will also own a small stake in the company.
TikTok accepted Oracle’s offer earlier this week over a bid from Microsoft, in which the company would have bought all TikTok operations in the United States, Australia, Canada, and New Zealand. Oracle’s close connections to the Trump administration could have played some part in the deal. While Oracle’s connections could improve the chances for approval in the United States, ByteDance confirmed this week that the deal will also need to be reviewed by the Chinese government to ensure it complies with recent updates to China’s export control list.
DOJ Announces Indictments Against Pro-Iran Hackers
The U.S. Department of Justice (DOJ) unveiled several indictments against pro-Iranian hackers this week. First, charges against two men, Behzad Mohammadzadeh and Marwan Abusrour, for hacking fifty-one U.S. websites following the killing of Qasem Soleimani were unsealed on Tuesday by the U.S. Attorney’s Office for the District of Massachusetts. “These hackers are accused of orchestrating a brazen cyber-assault that defaced scores of websites across the country as a way of protesting and retaliating against the United States for killing the leader of a foreign terrorist organization,” said Joseph R. Bonavolonta, special agent in charge of the F.B.I.’s Boston Division in a U.S. Department of Justice press release. Cyberattacks that deface websites are unsophisticated, and it appears that Mohammadzadeh and Abusrour were operating independently, not under the orders of Tehran.
On Wednesday, federal prosecutors accused two Iranian nationals of targeting U.S. computer networks and selling stolen data to the Iranian government and on the black market for personal gain. “Today’s defendants will now learn that such service to the Iranian regime is not an asset, but a criminal yoke that they will now carry until the day they are brought to justice,” said Assistant Attorney General John Demers in a statement.
In addition, on Thursday, the DOJ unsealed an indictment charging three Iranian hackers with stealing data from U.S. aerospace and satellite companies on behalf of Iran’s Revolutionary Guard Corps. The campaign is believed to have started in July 2015 and targeted companies in the United States and abroad. This week’s revelations by the DOJ are the latest examples of the U.S. government’s aggressive efforts to counter malicious cyber activity linked to Iran.
Facebook and Twitter Close Accounts Linked to Conservative Youth Group Disinformation Campaign
On Tuesday, Twitter and Facebook suspended over twenty accounts behind a months-long disinformation campaign run by Turning Point Action (TPA), a conservative youth group based in Phoenix. According to the Washington Post, the group paid American teenagers to use their personal social media accounts to spread false information, including tweets claiming that coronavirus numbers were intentionally inflated and mail-in ballots “will lead to fraud” in the upcoming presidential election, as well as a claim on Instagram that 28 million ballots went missing in the past four elections. According to parents of the teens involved, their kids found the work fun and received bonuses from TPA if their social media posts were widely shared. Graham Brookie, director of the Atlantic Council’s Digital Forensic Research Lab, said that the effort shows “that the scale and scope of domestic disinformation is far greater than anything a foreign adversary could do to us.”
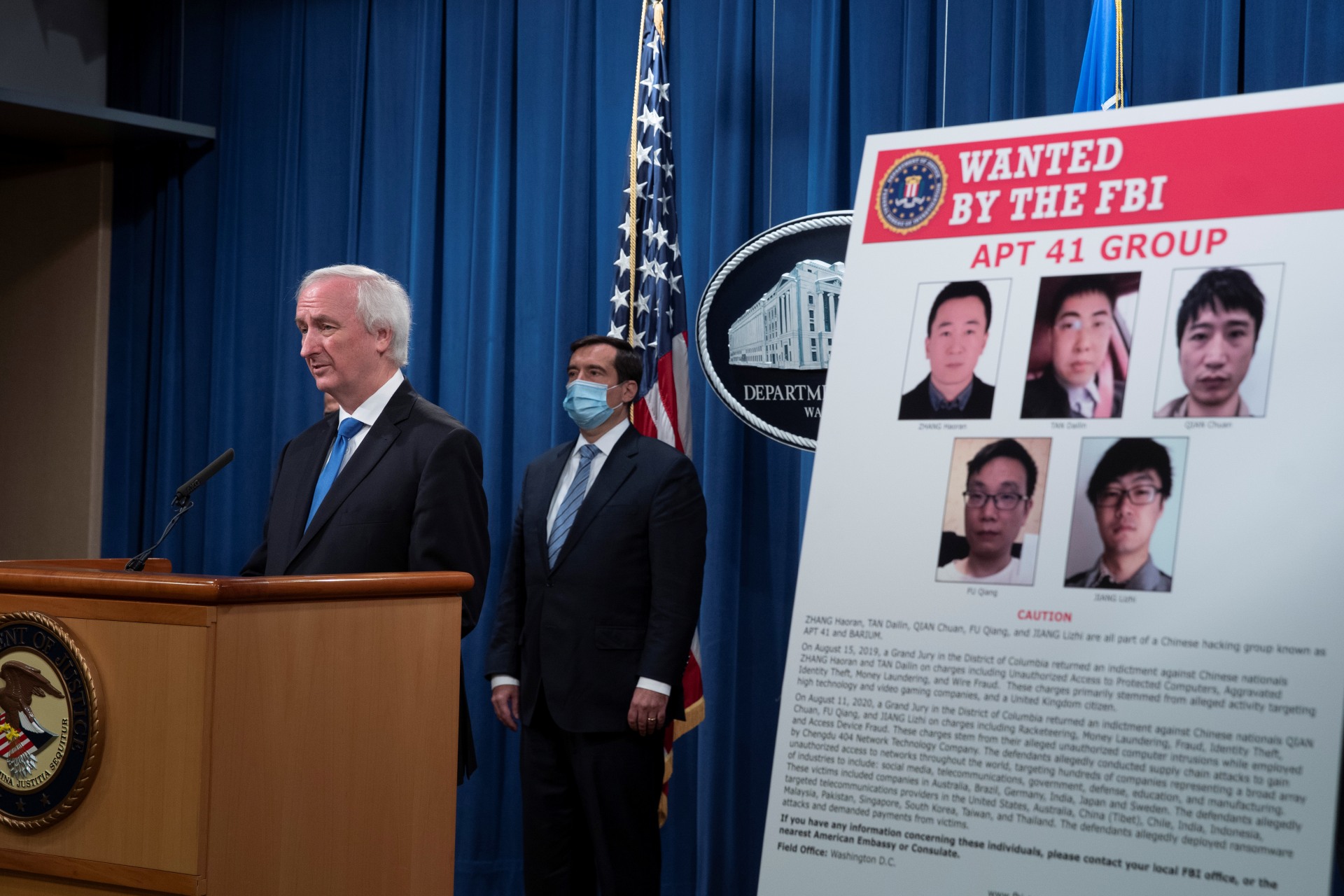
DOJ Charges Chinese Hackers and Two Malaysian Businessmen in Global Cybercrime Spree
On Wednesday, the U.S. Department of Justice (DOJ) announced charges against five Chinese citizens and two Malaysian businessmen accused of targeting over one hundred companies, human rights groups, and academic institutions globally since 2014. The alleged Chinese hackers are believed to be part of APT 41, a threat group affiliated with China’s Ministry of State Security (MSS). The Malaysian businessmen are accused of scheming with two members of the group to hack into video game companies to sell in-game currencies and items for profit. Most of the operations carried out by the defendants vary between stealing source code, customer data, and money, blurring the line between activities carried out at the behest of Beijing and for personal gain. According to communications between the hackers intercepted by the U.S. government, at least one of them bragged about their close relationship with the MSS and said they’d be protected by Beijing as long as they didn’t target Chinese networks. Echoing this, U.S. Deputy Attorney General Jeffrey Rosen condemned the Chinese government in his statements, saying it has a history of “making China safe for their own cyber criminals, so long as they help with its goals of stealing intellectual property and stifling freedom.” The charges are the latest in the Trump administration’s efforts to publicly denounce malicious Chinese behavior in cyberspace.
Ransomware Attack Could Have Led to Hospital Patient’s Death in Germany
On Thursday, German police launched a “negligent homicide” investigation after a patient scheduled for life-saving surgery at Duesseldorf University Hospital died following a ransomware attack that hit the hospital’s networks and infected over thirty internal servers, making the hospital’s systems inoperable. The justice ministry of North Rhine-Westphalia suggested that the patient died as a result of a delay in treatment caused by the attack. German authorities believe that the hospital was an unintended victim of the ransomware, as a note was found on one of its servers demanding that Heinrich Heine University contact the hackers. After being contacted by German police, the hackers withdrew their ransom demand and allowed the hospital to decrypt their systems. According to Ciaran Martin, former CEO of the UK’s National Cyber Security Centre, “if confirmed, this tragedy would be the first known case of a death directly linked to a cyber-attack. It is not surprising that the cause of this is a ransomware attack by criminals rather than an attack by a nation state or terrorists.”
