Hacking Charges Against Russian FSB Officers: A Quick Reaction
By experts and staff
- Published
 Adam SegalCFR ExpertIra A. Lipman Chair in Emerging Technologies and National Security and Director of the Digital and Cyberspace Policy Program
Adam SegalCFR ExpertIra A. Lipman Chair in Emerging Technologies and National Security and Director of the Digital and Cyberspace Policy Program
This post was co-written with Alex Grigsby, assistant director of the Digital and Cyberspace Policy program.
This morning, the U.S. Department of Justice (DOJ) announced the indictment of four people allegedly responsible for the breach of over 500 million Yahoo accounts the company announced last year. What makes this interesting is that two of the indictees are Russian intelligence officials working for the FSB--the successor to the KGB.
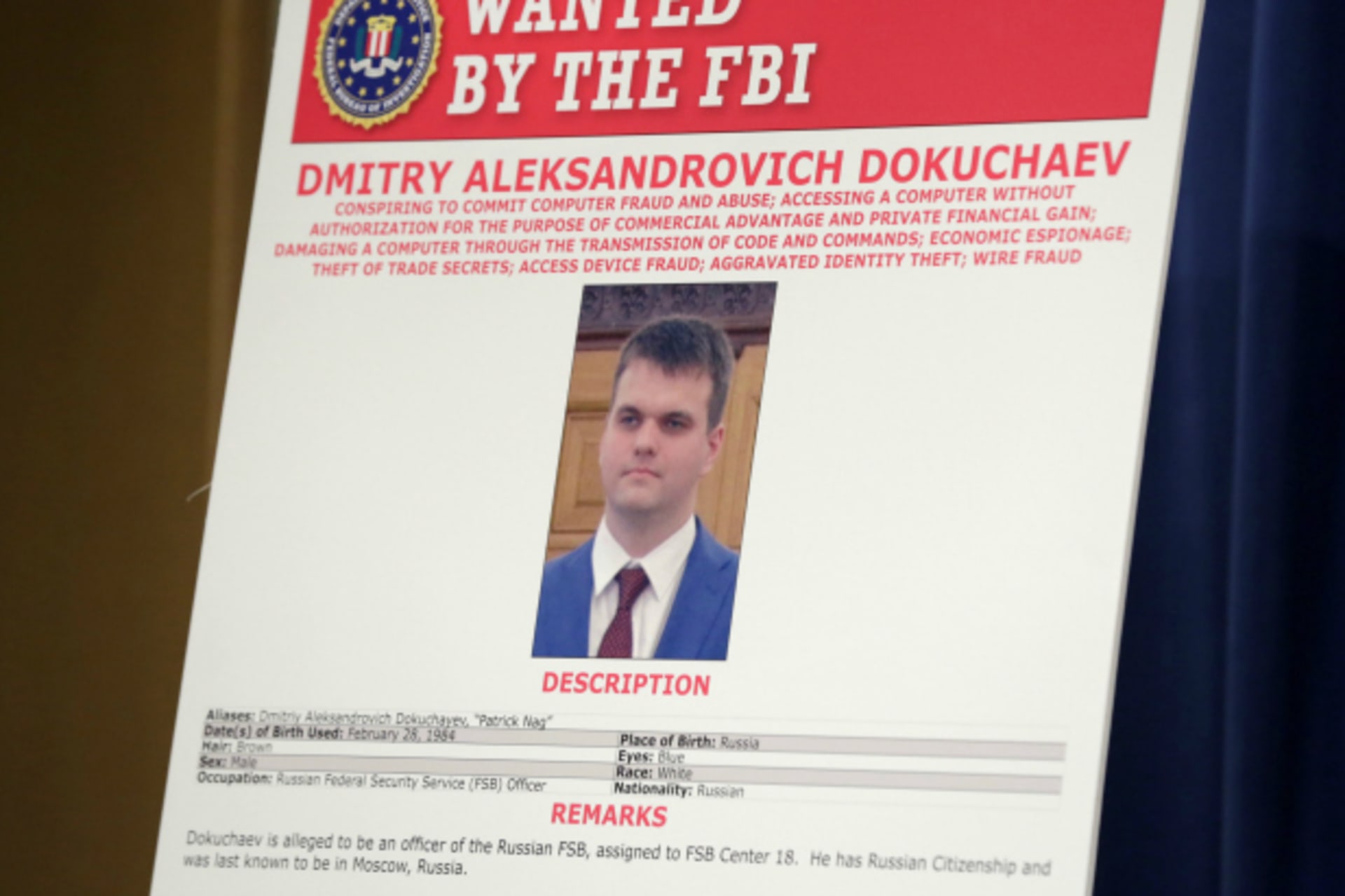
It looks like the Federal Bureau of Investigation (FBI) nabbed a pretty classic espionage operation. According to the indictment, two FSB officers--Dmitry Dokuchaev and Igor Sushchin--and Alexsey Belan--one of the FBI’s most wanted criminals and named in the sanctions President Obama issued against Russia in response to the DNC hack--obtained access to Yahoo’s user database. They then used that access to access the accounts of possible Russian intelligence targets, such as diplomats, investigative reporters, and representatives of U.S. companies. Dokuchaev and Sushchin also used the data to help Karim Baratov access approximately 80 accounts hosted by Google and an unnamed Russian provider. Baratov, a 22-year-old dual Kazakh-Canadian citizen living outside of Toronto, was paid for his services and liked nice cars.
The indictment also alleges that Dokuchaev and Sushchin helped Belan mine the Yahoo data for his personal criminal purposes, who searched compromised accounts for credit card details and gift cards either to use for himself or to sell in cybercrime forums.
There are a couple of significant differences between this incident and the other instances in which the U.S. government laid hacking charges on state-sponsored actors. In the 2014 indictment of the five People’s Liberation Army (PLA) officers, it was clear that China was not going to turn them over. In that case, the charges were probably more political--forcing China to reckon with seriousness with which the United States took the pilfering of its companies’ intellectual property. The 2016 charges against the Iranians affiliated with the Revolutionary Guards were probably less political, but nevertheless were partly meant to discourage Iranians from hacking U.S. targets lest it hinder their ability to travel and as a deterrent to future hacking, a sign that the United States could attribute attacks to individuals.
In this recent case, at least one of the indictees--Karim Baratov--is likely to see the inside of a U.S. court. Canadian authorities arrested him yesterday and he is likely to be extradited. There are a number of instances in the indictment that suggest U.S. authorities obtained evidence of the links between Baratov and the FSB by monitoring their communications. During a criminal trial, that would possibly require U.S. prosecutors to disclose how they monitored the conversations and under what authorities. In a recent case against alleged child pornographers, the DOJ chose to drop its charges instead of revealing how investigators exploited a vulnerability in the TOR network to identify the suspects. That could also happen here if Baratov contests the accusations. The DOJ could put pressure on Baratov to plead guilty to lesser charges to avoid that outcome. It is worth noting that in a previous hacking case, Su Bin, a Chinese national living in Canada, pled guilty to stealing information from U.S. defense contractors for the PLA’s consumption, making it unnecessary for the federal government to prove its case.
Another oddity with the case is the fact that Dmitry Dokuchaev was arrested earlier this year in Russia and accused with treason, along with the former head of the FSB’s information security center, Sergei Mikhailov and a former Kaspersky employee. It is unclear what Dokuchaev might have done that was treasonous in the eyes of the Russian legal system. One theory is that he was a CIA mole, which begs the question why would the U.S. file charges against one of its assets?Another could be that he hacked the wrong people while making a bit of money on the side, and got swept up for that.
The ripple effects will be felt on two fronts. First, these indictments obviously worsen and complicate the relationship with Russia in cyberspace. Some saw the Shadow Brokers leaks of NSA hacking tools in August 2016 as retribution for the attribution of the DNC hacks to Cozy Bear and Fancy Bear and as a warning shot across the bow, a reminder that Russia is a very capable actor in cyberspace. We will have to wait how the Kremlin decides to respond this time, but it is likely to be a mix of official and asymmetric actions.
Second, in announcing the indictments, the DOJ trumpeted the cooperation with Yahoo and other tech companies, and Yahoo did the same. For DOJ and FBI, this is a welcome change of messaging to Silicon Valley. The headline is not that law enforcement wants to weaken encryption and build backdoors in products, but that working closely with the government can result in taking down state-backed hackers that threaten the private sector. That message might resonate for a little, but long term tensions are bound to return.