Time to End the Dual Hat?
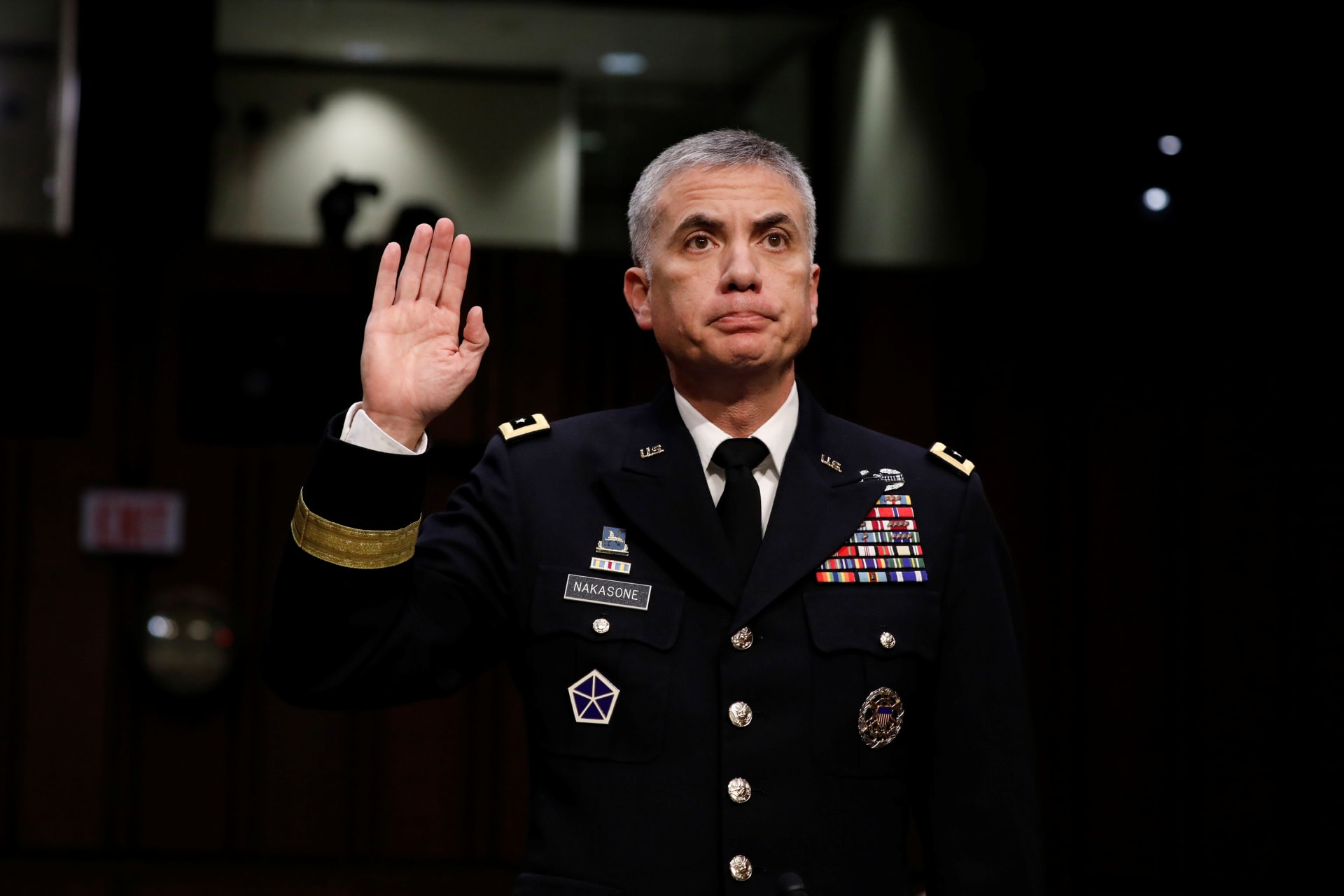
Following the SolarWinds breach, there have been renewed calls for the end of the dual-hat authority that governs the National Security Agency and U.S. Cyber Command.
By experts and staff
- Published
- Guest Blogger for Net Politics
Erica D. Borghard is a senior fellow with the New American Engagement Center at the Scowcroft Center for Strategy and Security at the Atlantic Council.
The extraordinary scope and scale of the SolarWinds breach, in which presumptive Russian threat actors gained access to dozens of federal government networks, have reinvigorated outstanding questions about the continued viability of the dual-hat authority structure that governs the National Security Agency (NSA) and U.S. Cyber Command. In the midst of revelations about the SolarWinds breach, it was rumored that the Trump administration would push through an end to one individual sitting at the top of the NSA and Cyber Command in the waning days of the administration. This hasty proposal garnered significant resistance, especially in Congress, and the four legislative commissioners on the U.S. Cyberspace Solarium Commission issued a statement strongly opposing the dual hat split. Yet, this is unlikely to be the end of the debate, and some have argued that, among other things, the NSA’s support to Cyber Command’s operational requirements could have inadvertently contributed to the intelligence failure of not anticipating or uncovering the SolarWinds incident. However, calls for the immediate separation of the dual hat are premature. The Biden administration should take a deliberate approach that weighs a number of important equities and concerns.
When Cyber Command was created in 2009 under U.S. Strategic Command, it was vested with a leadership structure in which the same individual—a four-star flag or general officer—would simultaneously serve as the director of the NSA with Title 50 authorities [PDF] and commander of Cyber Command with Title 10 authorities. The decision was likely made for a number of reasons. Cyber Command was a new organization with few resources, including personnel, access, and tools, and NSA could help it develop. There is also a high potential of overlap between military and intelligence operations in cyberspace and a dual-hatted leader could deconflict and reconcile competing prerogatives and interests across NSA and Cyber Command.
How long the dual hat would last was always uncertain. For instance, in 2016 there were reports that the Director of National Intelligence and Secretary of Defense at the time were recommending its separation. However, in the 2017 National Defense Authorization Act (NDAA), Congress established in law specific conditions to be met—to which the Chairman of the Joint Chiefs of Staff and Secretary of Defense would have to certify—that would enable the dual hat’s separation to proceed. The question of separation remerged in 2018 after Cyber Command was elevated to a unified combatant command and the Cyber Mission Force achieved full operational capability. However, in the 2020 NDAA Congress amended the existing requirements to raise the bar for its split. Of note, Congress added an additional requirement beyond Cyber Command achieving full operational capability—which at that point had already occurred—to include having a demonstrable capability to carry out all of the Defense Department’s missions in cyberspace. Congress also strengthened the requirement for Cyber Command to be able to develop its own accesses and capabilities. At this point, there has been no certification to Congress that the conditions specified in law have been met.
Separating NSA and Cyber Command is more of a question of “when” than “if.” Since its establishment, Cyber Command had considerably developed in terms of organization, personnel, capabilities, and operational experience. At the same time, with the introduction of the “defend forward” [PDF] concept, in which cyber forces maneuver outside of U.S.-controlled cyberspace, the scope of its mission has expanded—as have the demands placed on the NSA for tactical intelligence support to Cyber Command’s operations. Given this, the responsibility for both an operational combatant command with a growing mission set, as well as an intelligence agency with critical cryptological and signals intelligence missions, could be optimally performed by two distinct individuals rather than one.
That said, the Biden administration will have significant discretion to shape the timing and sequencing of what is likely an inevitable split of the dual hat. While the law does stipulate six conditions that would need to be met to precipitate the dual hat’s separation, Congress did not provide much guidance in terms of metrics corresponding to those conditions. In other words, the type of evidence that would confirm or deny Cyber Command’s operational maturity remains underspecified, giving considerable latitude to the executive branch to shape the timing and conditions under which certification would occur.
In evaluating these issues, the Biden administration should take into account three considerations. First, given the implications of the SolarWinds breach, it should immediately conduct a comprehensive review of the SolarWinds intelligence failure, to include assessing the extent to which competing Cyber Command and NSA equities over the prioritization of military versus intelligence missions could have played a role. Second, it should develop measures of effectiveness for Cyber Command that go beyond existing readiness metrics to inform decision-making around the timing of the split. Finally, pursuant to the 1986 Goldwater-Nichols Act, the NSA is designated as a combat support agency to provide intelligence support to military operations. In the context of dual-hatted authorities, this function is inherently integrated into the NSA-Cyber Command structure. Therefore, in assessing the conditions under which to separate the dual hat, the Biden administration should conduct a review of how NSA would function in its combat support agency role when split from Cyber Command and provide recommendations to preserve the continuity and institutionalization of that role.
Taken together, this suggests that, while there are compelling reasons consider splitting the dual hat, the road ahead should be slow and methodical.